The Ethical Hacker’s Toolbox: Methods and Instruments for Goodness
from web site
During today's digital age, the significance of cybersecurity cannot be emphasized. While technology keeps to advance, so too do the tactics employed by cybercriminals to take advantage of vulnerabilities and execute attacks. This growing landscape of digital threats has led in a heightened demand for ethical hackers—professionals who utilize their skills and knowledge to defend systems rather than jeopardize them. The role of an ethical hacker is essential in strengthening defenses and developing robust cybersecurity strategies that can withstand the complexities of modern threats.
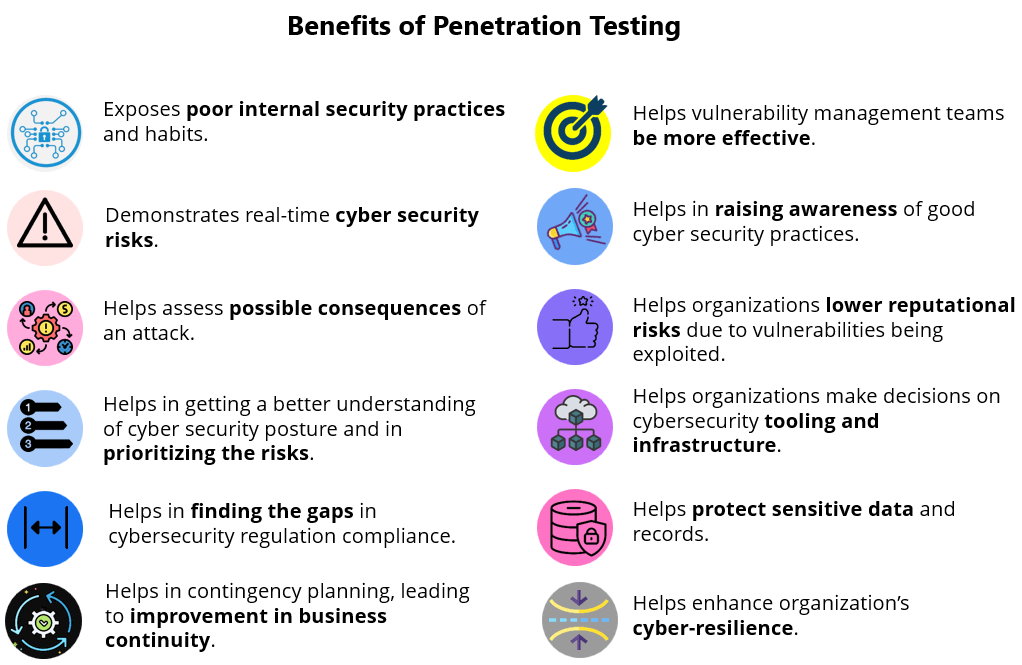
At the core of ethical hacking lies a diverse toolbox filled with techniques and tools designed for proactive cyber defense. From penetration testing to security vulnerability testing, these methodologies not only detect weaknesses but also offer a roadmap for organizations to strengthen their defenses. By grasping the tactics used by malicious actors, ethical hackers work tirelessly to ensure that sensitive data remains secure and that systems function without disruption. The journey into ethical hacking reveals a vibrant field dedicated to safeguarding our digital world while upholding the principles of integrity and accountability.
Crucial Resources for Penetration Testing
In the realm of ethical hacking, penetration testing is essential for identifying security flaws before threat actors can take advantage of them. A variety of solutions are offered to aid ethical hackers in conducting attacks and reviewing the safety of systems. One of the most popular tools is the Metasploit Framework, which offers a robust framework for creating and performing exploits against a designated target. With its comprehensive library of attacks and input payloads, Metasploit allows ethical hackers to evaluate security gaps and assess the strength of established security protocols.
Another vital tool in the pentester's toolbox is Nmap, a robust network discovery tool that allows users to discover devices and applications on a network. Through its different scan types, Nmap provides data into the operating systems, open ports, and services in operation of hosts within the network. This information is essential for developing a thorough knowledge of the exposure and prioritizing risks that need to be addressed during the pentesting process.
The Wireshark tool is also an essential tool for ethical hackers, operating as a network protocol analyzer that collects and inspects packets of data in live. By evaluating the data flowing through the network, pentesters can uncover vulnerabilities related to data transmission and security of the network. Cybersecurity Strategies make it crucial for investigating network discrepancies, identifying potential breaches, and confirming that information is sent safely across the network. Together, these tools form a strong foundation for efficient penetration testing and forward-looking information security.
Robust Cyber Security Strategies
In the constantly changing landscape of digital threats, organizations must adopt efficient cyber security tactics which not only safeguard their assets but also ensure the safety and privacy of sensitive data. One key approach is the adoption of regular pen-test testing. By simulating real-world assaults, ethical hackers can identify vulnerabilities before harmful actors take advantage of them. This proactive measure helps companies comprehend their protection status and bolsters defensive mechanisms against possible breaches.
Another crucial aspect of a robust cybersecurity approach is continuous safety weakness testing. This includes regularly scanning systems and applications to spot weaknesses that could be exploited by cybercriminals. By designating dedicated groups or utilizing digital tools, organizations can maintain a vigilant approach against developing threats. Additionally, embedding security into the software development lifecycle can resolve vulnerabilities early in the development process, minimizing threats in launched applications.
Finally, nurturing a security-conscious culture within an company is essential for efficient cybersecurity tactics. Training employees to identify manipulative attacks and deceptive attempts can significantly minimize the likelihood of successful breaches. Encouraging open communication about safety issues and including cyber security education into routine operations ensures that all employees of an business assist to its protection. By combining these strategies, organizations can create a strong framework that resists the challenges posed by the constant threat of online attacks.
Active Protection Confronting Digital Risks
In the current interconnected world, digital threats are constantly changing, making it essential for organizations to adopt preventive defense strategies. White-hat hackers serve a vital role in identifying vulnerabilities before they can be exploited by malicious actors. By executing regular penetration testing, organizations can emulate actual attacks, assess their safety posture, and implement necessary upgrades to their security frameworks. This proactive approach ensures that potential weaknesses are tackled in advance, minimizing the risk of breaches.
In addition to penetrating testing, organizations can benefit from comprehensive security vulnerability testing, which identifies and assesses potential security flaws within their infrastructures. White-hat hackers utilize various tools and approaches to carry out these tests, pinpointing areas of issue that might otherwise be missed. By prioritizing and remediating these vulnerabilities, companies can fortify their defenses against a diverse range of digital threats, thereby protecting sensitive data and assets.
In conclusion, an effective preventive cyber protection strategy should involve ongoing monitoring and assessment of security measures. Threat landscapes can vary dramatically, and ongoing alertness is key to maintaining a robust security posture. By leveraging advanced analytics and threat intelligence, white-hat hackers can help organizations remain ahead of emerging threats, ensuring that their cybersecurity strategies evolve in tandem with the difficulties posed by harmful actors. This commitment to preventive defense is crucial for fostering a strong cybersecurity environment.
